Orbit 60 Series Update: Cyber Secure Condition Monitoring!
Welcome back for our first quarterly update of Orbit 60 for 2021. Orbit 60 is Bently Nevada’s latest state of the art condition monitoring, protection and data integration platform. In last quarter’s update, we discussed the enhancements made in our Output cards, and how we aXessTM System 1, conneXTM to your DCS/Historian and output to your remote display(s).
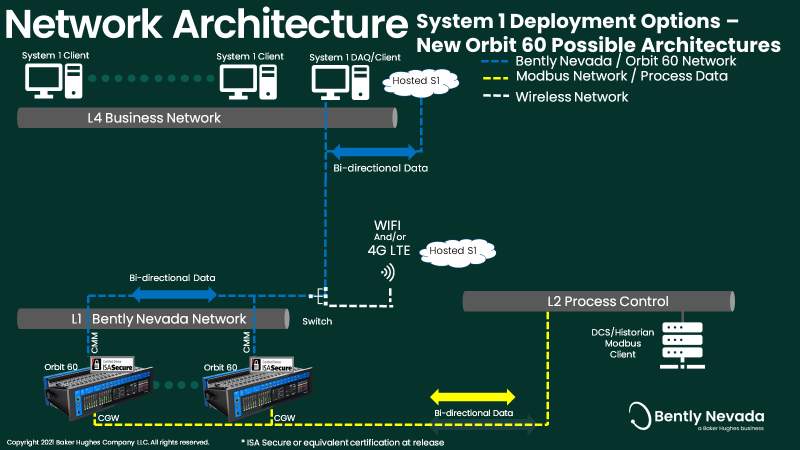
In this update, we will discuss in greater detail, how we aXessTM System 1 with the Condition Monitoring Monitor Module, CMM, specifically emphasizing its inherent Cyber Security capabilities; how Orbit 60 also allows you to have multiple CMMs in one system, and how all of these expanded capabilities save you time and money in your deployments. A future article will cover our XtendTM feature of connecting multiple chassis, and utilizing remote I/O to further save you a significant deployment costs when installing the Orbit 60 system in your facility compared to other technologies. Just a quick note to remind you that some of the functionality discussed in this article may not be available at first release, but is firmly in our product roadmap for future enhancement.
In today’s environment, everyone is wary of hackers, and the damage their cyberattacks can instigate. Some hackers are motivated by the challenge and/or monetary rewards involved, but there are also “state sponsored” hackers that have funding behind them and are tasked with causing economic, reputational or even terroristic damage.
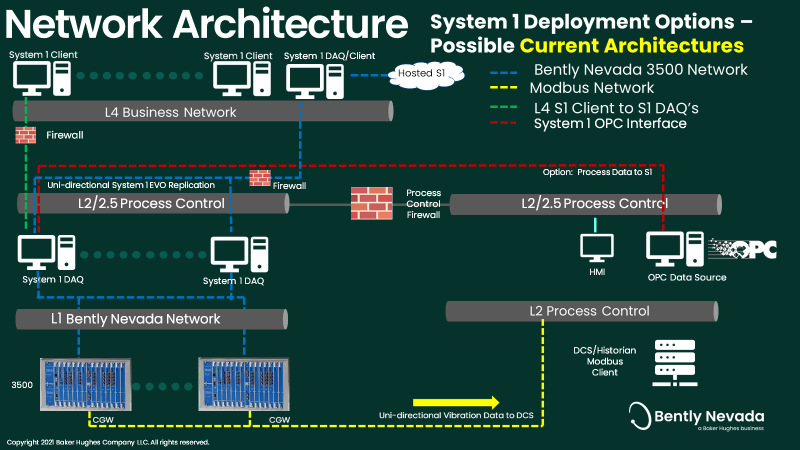
NERC, CIP, FERC as well as many Industrial Insurance policies require that any system that can change or interrupt the operation of a machine, such as the ability to trip it, be secure. Operationally, most of our customers accomplish this by isolating the controls and protection systems on networks that cannot access the internet. These networks are typically referred to as the L1 (Bently Nevada Network) or L2/2.5 (Control Network).
Typically, Bently Nevada’s System 1 server will sit on the L2/2.5 network (see figure 1) which allows the System 1 server to communicate with the plant’s 3500 racks as well as the process historian. This works well from a data collection point of view, in that System 1 has access to all of the vibration and process data (when that option is configured). The problem though, is the System 1 data cannot be accessed on the business (L4) network! Since this is where you, the user, resides most of the day, unless appropriate data diodes, complex firewalls or data replication (System 1 EVO only) are incorporated into the network structure, access becomes difficult.
This means that some System 1 users will have to make their way from their office to the control room, or on occasion into a locked room (usually windowless, and tucked away in an inconvenient location) to view System 1 data, or make changes to its sampling parameters. Obviously, this is not ideal, and does not lend itself to on the fly diagnostics, or even proactive Condition Monitoring.
Given these issues, it is easy to see why, when we consulted with our customers, their number one concern was “making the new system cyber secure.”
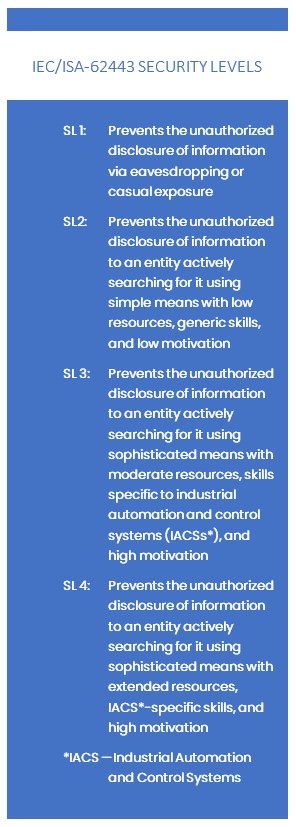
To that end, we have spent considerable time and effort to make Orbit 60 cybersecure. In fact, where possible, we have designed Orbit 60 to meet Security Level 4 (the highest level) of the IEC/ISA-62443 Standard1.
In 3500, which was initially designed prior to the advent of widespread cyber-criminal activity, the configuration tool and the communication tool were housed on the same card (3500/22). This made it impossible to physically separate them from one another, which led to additional measures or precautions to be in place when connecting System 1.
In Orbit 60, we have separated these two functions from each other. Each Orbit 60 system will have one System Interface Module, SIM, no matter how many other chassis are included in the system. The SIM is a vital component of the system and is where users log in and configure the system. We have discussed this in past articles, but it bears repeating, that in Orbit 60, we have hardened the configuration so that each user has their own credentials and therefore may have different permissions depending upon what the overall system administrator decides is appropriate for their role. Any changes to the system are time stamped and logged with the name of the person making the changes. Further, just like on the 3500 rack, there is a removable key that allows users to set the system on “Run” mode, locking out the ability to make any configuration changes, even if the user has otherwise proper credentials. Please note that even when the key is in “Run” mode, users may still log in and view diagnostic logs and access current values, they just will not be able to make any changes that could interrupt machinery operation.
1See Sidebar for IEC/ISA-62443 Security Levels
The SIM is also the heart of our Secure Boot system. It is in the SIM that we authenticate all of the various modules and their firmware. Orbit 60 Firmware images are protected using Secure Boot. Bently Nevada utilizes a highly secure third-party Public Key Infrastructure (PKI) provider to store and protect our private keys. When an Orbit 60 “smart” module is manufactured, the public portion of the key pair is placed in secure storage on the device. Every time a module is powered on and firmware is executed on the Orbit 60 device, the hash signature is checked against the embedded public key on the device to confirm that it is authentic Bently Nevada firmware that has not been tampered with or altered.
For further details, please see our white paper on Orbit 60 Security.
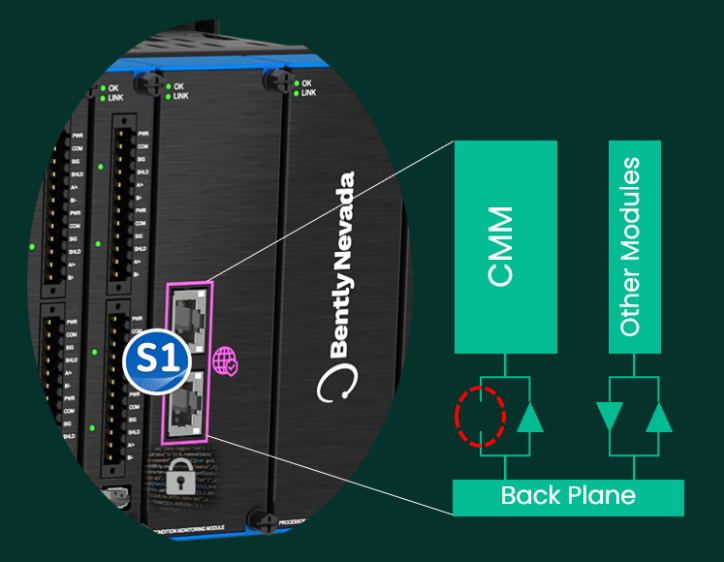
For communication with System 1, there is a separate, dedicated, Condition Monitoring Module, or CMM. This module has a patented design to provide READ ONLY “aXessTM” to all of the data on the backplane of the monitor system. This includes the raw waveforms (including for the first time, Keyphasors®!), calculated variables, alarm statuses, and process data, if the Communications Gateway is enabled for two-way “conneXTM” communication (also a new feature of Orbit 60 detailed below).
Effectively, our CMM can only listen to what is being broadcast to the backplane, but it has no ability to talk to it. Or, another way – Constantly listening, never talking. From an electronics point of view, the CMM has receivers, but no transmitters (or transceivers – which can talk as well as listen). This patented, unique, architecture ensures that all communication is unidirectional, and is always in a direction away from the backplane.
For further details, please see our white paper on Orbit 60 Condition Monitoring Module – Data Security.
Many folks are familiar with our 3500/92 Communications Gateway. This gateway serves data to the control system via Modbus. With Orbit 60 we have designed the system to not only serve measurement ,status and alarm data, but also to be able to request process data as well in a future release, which is referred to as Orbit conneXTM Due to the cyber security capabilities built into the Orbit 60 system, this exchange of data is also secure! The process data becomes just another stream of data available on the Orbit 60 backplane. We see three projected use cases for this information:
- The processing module can use this data to determine the machine’s state, i.e. is a pump storage generator in pumping or generating mode.
- That state can be used to process pre-configured alarm values, i.e. if it is in pumping mode, it may have different alarm and shutdown values than if it is generating.
- Data that is stranded on the control side of the network can be securely brought onto the business network without additional firewall infrastructure, providing you with a connection to your otherwise stranded data.
TLS 1.3 is the latest version of the TLS protocol and is a higher level of encryption security than that used by most banks. Many banks that use apps on your iPhone or Android still using TLS 1.2 to secure your transactions. TLS 1.3 is used to encrypt, and protect the communication between the configuration software, Orbit Studio, and the physical SIM. TLS 1.3 Encryption is automatically enabled between the CMM and System 1, however, if desired, encryption can be turned off.
When logging in to the Orbit 60 system to make configuration changes, view system logs, etc. the user must have local user credentials (username, password). Sensitive information, such as credentials are always encrypted so that no one can steal this information (no credential harvesting!).
The credentials give the users permissions to do certain tasks. For example, an operator role may not have permission to change relay logic or setpoints. The System Administrator is able to add, manage and remove specific users. A later release will allow you to setup a company-wide active directory login model for Orbit 60 systems, which will be handy in the case where a person leaves the company. When their permissions to utilities such as email are revoked, their access to Orbit 60 will also be automatically revoked as well. All without having to go to each individual SIM to revoke access.
The Orbit 60 is designed to tolerate attacks on the system, such as Denial of Services, Fuzzing and bad ethernet grammar. These are some of the common attack mechanism employed by bad actors to confuse and override systems.
As mentioned previously, any changes to setpoints or sensor configurations are logged with what changes were made, and who made them. The logging feature also captures all logins, and whether they were authorized or if improper credentials were used to try and break in. Your IT folks can use this to determine if a bad actor is attempting to gain access.
A future enhancement will be the logging of authorization events, such as who grants other user’s permissions.
Here the administrator will be able to setup rules for password complexity, such as length, special characters, etc.
- Module Decommissioning – If a module is removed from service, its memory can be wiped so that if the module is reused at another site, it will not retain any sensitive site information.
- Certificate Enforcement – This could be employed with third party (OEM’s) or others, that are granted aXessTMto the CMM(s).
- SYSLOG Support – System Information and Events Manager, SIEM, - In this scheme all SIEM events are automatically sent to a System manager (IT) for their evaluation. i.e. if an unauthorized person tries to log in, it would be available here for detection by the IT dept.
As described in this article, Orbit 60 is setting the new cyber security standard for condition monitoring, protection, and data integration. Every Orbit 60 system that is manufactured has all of these security features built in by default and any improvements made over time will be available with a simple firmware upgrade. The architecture of Orbit 60 allows for endless deployment models and is built for long-term support and flexibility to adapt to new security standards in the future.
More information is available on our website.
Fall 2019 – Public disclosure and new product announcement (ATD)
Spring 2020 (April) - Available to quote (ATQ) fixed price proposals
Spring 2021 (April) – Available to ship (ATS) API Turbomachinery and plantwide applications
Summer 2021 (August) – Available to ship (ATS) TSI and Bridging applications
Our teams are excited to discuss Orbit 60 in more detail, we have multiple technical white papers available for a deeper dive into the following topics. Please reach out through the contact us link below to receive a copy and we will connect you with your local expert.
- Orbit 60 Series or 3500 Detailed Comparison - This document details the difference between Bently Nevada’s Orbit 60 Series machinery protection system and the 3500 system.
- Orbit 60 Data Security Condition Monitoring Module - This document is intended to describe how the Condition Monitoring Module in the Orbit 60 Series Monitoring System provides a secure solution with full high-resolution data to external networks without jeopardizing the operation of the protection functions.
- Orbit 60 Series Bridging Concepts - Bently Nevada introduces the concept of bridging with the Orbit 60 Series system architecture.
Product Video - Orbit 60 Teaser
Product Video – Orbit 60 Full length
Orbit 60 Series and System 1: Bloomberg TV
Houston Chronicle: Bently unveils the Orbit 60
Turbo Machinery Magazine – Bently Nevada’s New Platform
Q1 2020 Orbit Article – Introducing Orbit 60
Q2 2020 Orbit Article – Available to Quote – Explore the Cost Savings
Q3 2020 Orbit Article – Now – Less Spares!! – How to Choose Input Modules
Q4 2020 Orbit Article - Orbit 60 Series Update: System Fundamentals - Output Cards

Tarannum Sarang
Senior Product Manager

John Kingham
Strategic Field Application Engineer
BIO
Mr. Kingham has been involved in the rotating machinery realm for more than 35 years. He started with Bently Nevada in 1986 as a Machinery Diagnostics Engineer, where he diagnosed machinery problems based upon their vibration characteristics.